Devices that were infected by the first stage automatically accessed the malicious string at the end of the URL. From there, they were infected with a second stage.
The video on Vimeo worked similarly, except that the string was included in the video description.
Ars representatives had nothing further to add. Vimeo representatives didn’t immediately respond to an email.
The campaign came from a threat actor Mandiant tracks as UNC4990, which has been active since at least 2020 and bears the hallmarks of being motivated by financial gain. The group has already used a separate novel technique to fly under the radar. That technique spread the second stage using a text file that browsers and normal text editors showed to be blank.
Opening the same file in a hex editor—a tool for analyzing and forensically investigating binary files—showed that a combination of tabs, spaces, and new lines were arranged in a way that encoded executable code. Like the technique involving Ars and Vimeo, the use of such a file is something the Mandiant researchers had never seen before. Previously, UNC4990 used GitHub and GitLab.
The initial stage of the malware was transmitted by infected USB drives. The drives installed a payload Mandiant has dubbed explorerps1. Infected devices then automatically reached out to either the malicious text file or else to the URL posted on Ars or the video posted to Vimeo. The base 64 strings in the image URL or video description, in turn, caused the malware to contact a site hosting the second stage. The second stage of the malware, tracked as Emptyspace, continuously polled a command-and-control server that, when instructed, would download and execute a third stage.
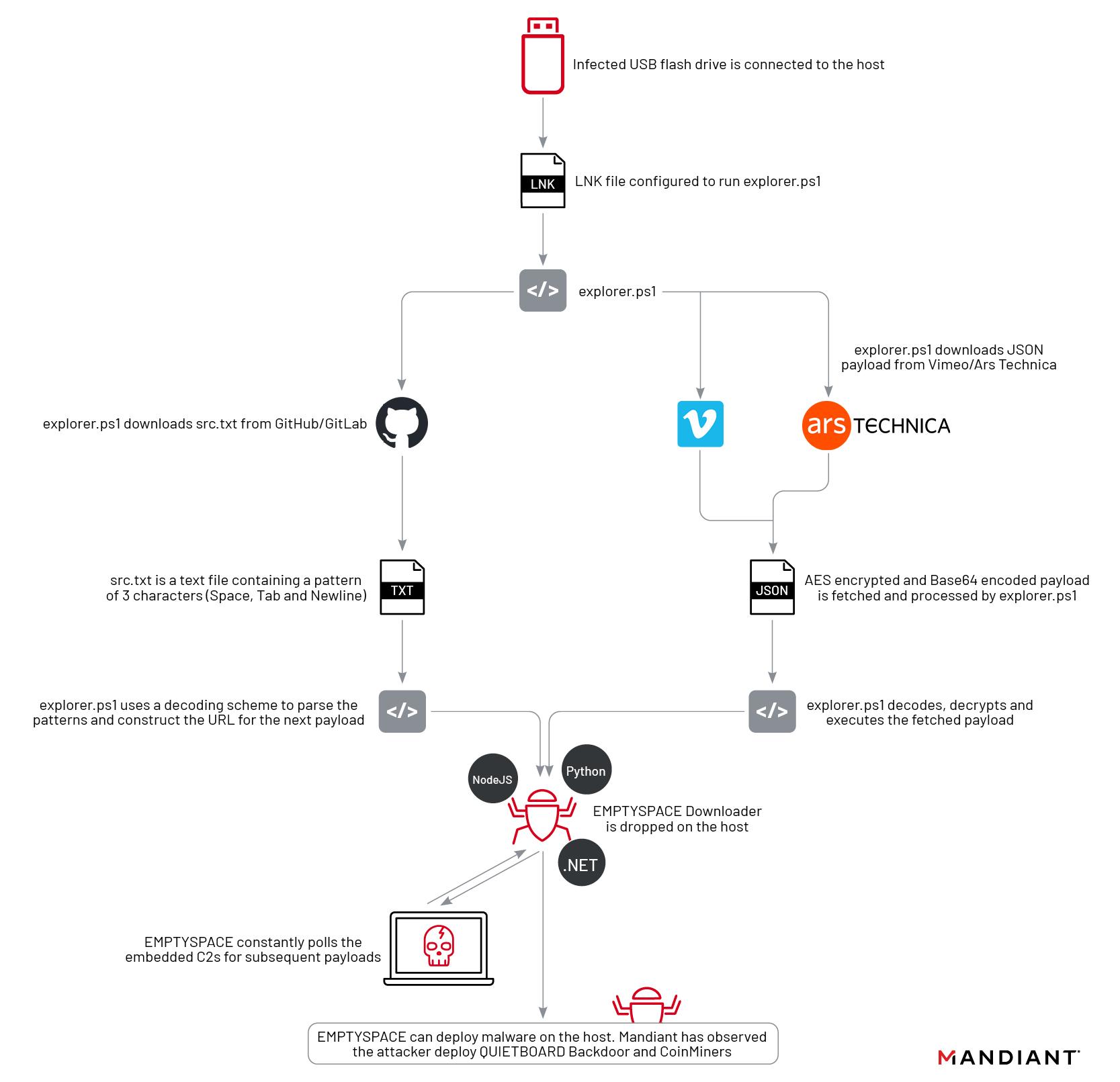
Mandiant has observed the installation of this third stage in only one case. This malware acts as a backdoor the researchers track as Quietboard. The backdoor, in that case, went on to install a cryptocurrency miner.
Anyone who is concerned they may have been infected by any of the malware covered by Mandiant can check the indicators of compromise section in Tuesday’s post.